Acronis True Image 28.2.2 Crack + Serial Key Full Version
Acronis True Image Crack is the most capable computer backup solution, including all of the functions and tools required to backup data or information. The bootable ISO has improved thanks to a high-performance technology that can backup the program, configuration, and other Windows information on the software. It was also designed with simplicity in mind. After installation, launch the app and choose Free Trial.

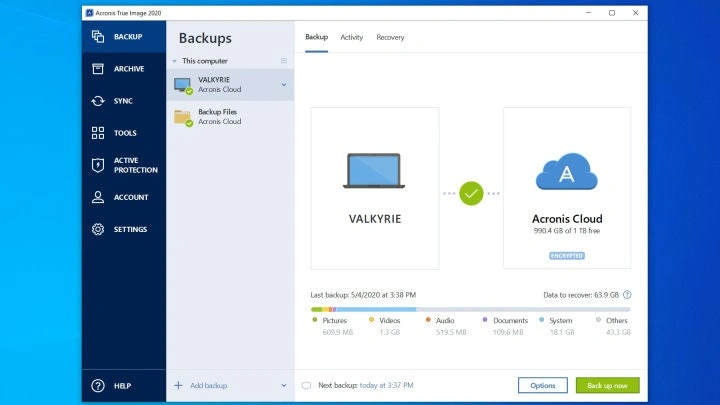
Acronis True Image Mac is supports all forms of media, including photos, images, documents, videos, and information. Users can restore or backup data as needed. If there are any changes to the folder, the application allows the user to specify a specific folder for automatic backup. The application is compatible with machines running Windows XP and later versions of the Windows operating system. It made the backup process more convenient and streamlined, saving time and effort.
You Can Also Download: iBackupBot
Acronis True Image 28.2.2 Crack & Keygen Full Version
Acronis True Image Free a graphical user interface for enhanced visual impacts and comprehension. it allows you to import and export backup settings from ZIP files, as well as convert Acronis backups to Windows backups and vice versa. The resulting picture file is compatible with FAT16, FAT32, and NTFS. Users can also create a boot image for Windows.
Acronis True Image Cracked is well-known in the Windows world for its True Image drive-imaging application, and this is its attempt to enter the Mac market. Its key advantages are its versatility and simplicity. It supports both local and cloud-based backups, as well as any network-attached drive that isn’t specially designed to function with Time Machine. You’ll need an Acronis account to access your ‘unlimited’ cloud storage space with Acronis’ online backup service, but you may still backup to a network or other local device.
You Can Also Download: Adobe Audition CC
Key Features of Acronis True Image Portable:
- A backup application with all of the features and tools.
- Can create a boot image for Windows.
- The generated picture file is compatible with FAT16, FAT32, and NTFS.
- It can handle photographs, images, documents, movies, and other types of data.
- Recover wherever you are, even if your operating system fails.
- 2TB+ drives protect more than two terabytes of files, programs, and other content.
- It allows the user to specify a folder for automatic backup.
- Can restore or backup data as needed.
- You may import and export backup settings between ZIP files.
- Enjoy speedier performance and a more straightforward interface.
- Get any file from your cloud backup.
- Provides blockchain data notarization.
- Mirror imaging. Disk cloning. All-in-one recovery drive. Acronis True Image Activation Key ensures
- that your data is always available for recovery, no matter what happens.
- Any file from the cloud backup can be retrieved on any device, regardless of location. Manage
- backups remotely. Experience safe file synchronization and sharing.
- The first personal backup solution that uses AI to detect and prevent ransomware and password
- hijacking in real time. Offer blockchain data notarization.
- The way we access and use data changes all the time, as do the threats to it. Your protection must also improve.
- With over 100 upgrades and new features, it keeps you current.
You Can Also Download: WebcamMax
PROS:
- More backup tools than any other app
- Local and cloud backup options
- Full disk image backup and restore
- Includes file syncing
- Protects against ransomware and malicious URLs
CONS:
- Some cutting-edge technology may be risky to use
- Disk-cloning feature didn’t work in our tests
- Performance issues with the upload speed and mobile apps
- Poor phishing and middling malware-blocking results
System Requirements:
- Operating systems supported include Windows XP, Vista, 7/8, 8.1, and 11.
- Memory (RAM): 1 GB of RAM is required.
- 1.5 GB of free hard drive space is required.
- CPU: Intel dual-core CPU or later.
How to Install?
- First, get Acronis True Image Crack full version.
- Uninstall the previous version with IObit Uninstaller Pro.
- Note Turn off Virus Guard.
- After downloading, unpack or extract the RAR file and run the setup.
- Install the setup; after installation, it closes from everywhere.
- Now, open the ‘Crack’ or ‘Patch’ folder, copy and paste the patch into the installation directory, and apply it.
- Please use the registration activation file.
- After all of this, you can enjoy the latest version.